Google Pixel 10 Pro XL
Big screen. Serious power.
Experience end-to-end encrypted messaging like never before. No identifiers, no trackers, no compromise.
Start your journey to a secure and private communication today.

Get fully protected in three simple steps. No technical knowledge required.
Select from our range of hardened Google Pixel devices, pre-loaded with CryptoChat OS and all security tools pre-configured out of the box.
Your local reseller configures the entire device and activates your subscription, so it is ready to use immediately with zero setup required by you. Resellers cannot tweak or change any system settings, ensuring your device's integrity remains completely intact.
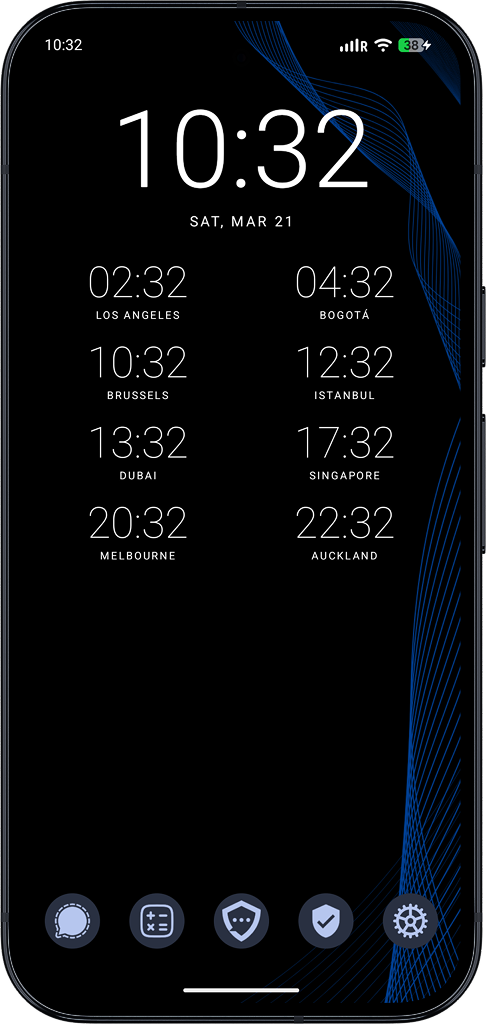
Send encrypted messages, make private calls, and share files — all protected by end-to-end encryption, with zero metadata and zero traces.
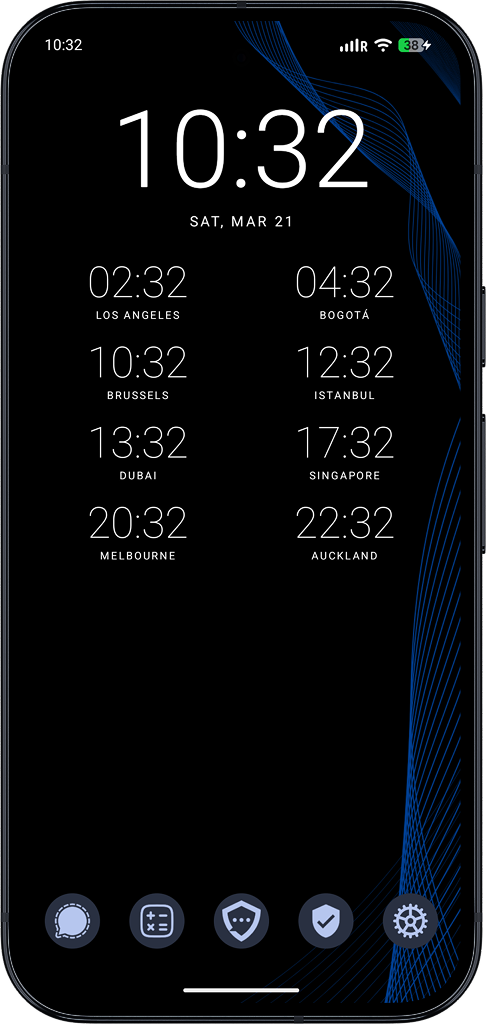
From the OS up to the network — every component is hardened and designed to protect you.
Our custom operating system strips away telemetry, closes attack vectors, and enforces strict sandboxing at the kernel level — far beyond what stock Android or iOS offers.
Explore featuresYour messages travel through multiple encrypted relay nodes across privacy-respecting jurisdictions. No single server ever knows both who you are and who you're talking to.
View architectureHybrid X3DH Double Ratchet Encryption and post-quantum encryption ensures your communications are safe today — and future-proof against quantum attacks.
Learn moreUse the map or country list to inspect supported networks and confirm whether LTE and 5G are available before you travel or deploy devices.
No supported countries match your search.
We focus on what matters most, keeping your conversations private, your data secure, and your experience effortless. Our platform is built with military precision, combining advanced security and encryption with a seamless user experience. No compromises, no unnecessary complexity and useless features just powerful, reliable communication and top notch security at every level.
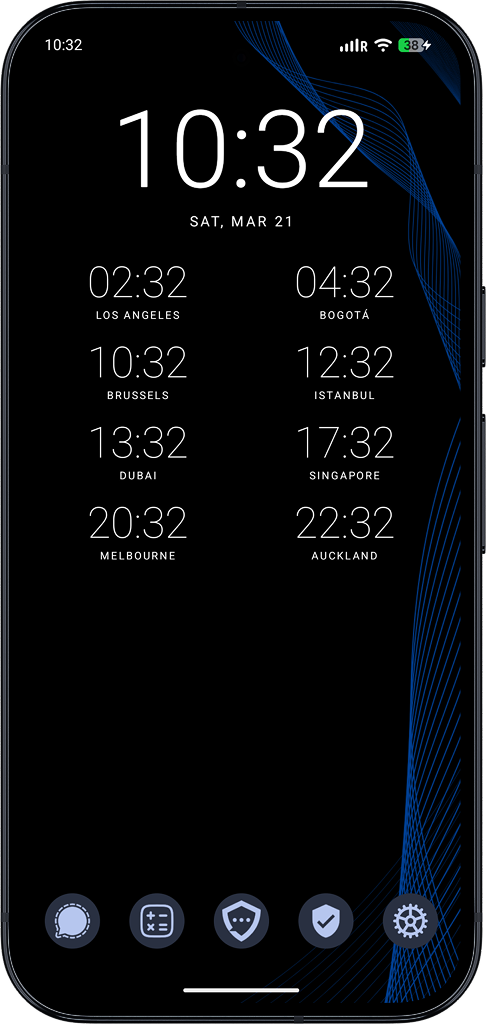
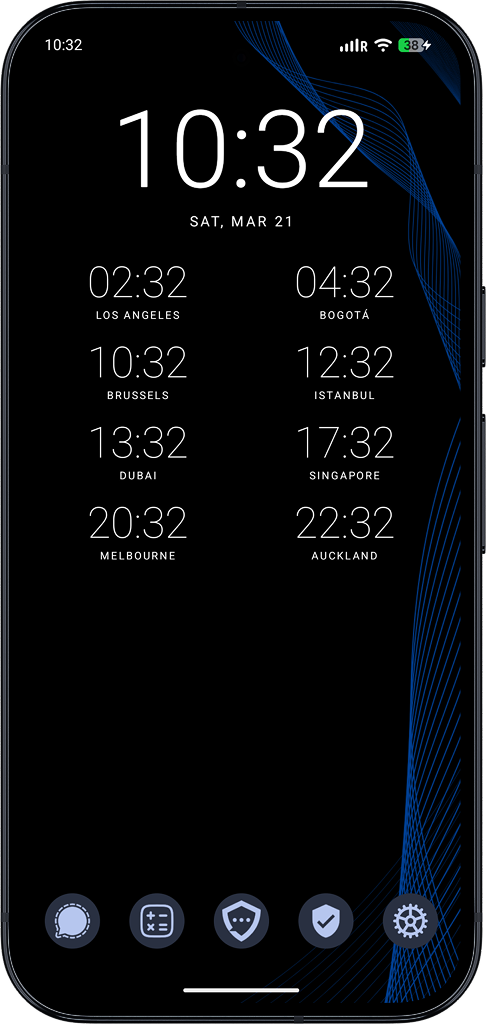
Encrypted Google Pixel devices pre-installed with CryptoChat software
Big screen. Serious power.
Pro-grade everything
Flagship performance, perfect size
Perfect balance of power
Best value security
Compact flagship
Affordable security
Next-gen value

Short term access

Most popular choice
Maximum savings
Need pricing, regional availability, or a direct point of contact before ordering? Visit our reseller page to connect with the right team.
Our advanced security architecture protects against everything from low-level threats to sophisticated adversaries. Multiple layers, including Extended Key Exchange, Post-Quantum Encryption, Multi-hop Routing, and Double Ratchet encryption to ensure your messages remain private and secure at all times.
See why our privacy-first approach outclasses mainstream messaging apps.
| Feature |  Signal Signal |
 WhatsApp WhatsApp |
 Google Messages Google Messages |
 Apple iMessage Apple iMessage |
 Element Element |
 Telegram Telegram |
 Threema Threema |
 Viber Viber |
|||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Recommended | GREAT | OK | OK | No | No | No | No | No | No | OK | No |
| Encryption by Default | |||||||||||
| Ships on Hardened OS | |||||||||||
| Anonymous Signup | |||||||||||
| No Directory Server for Contacts | N/A (RCS) | ||||||||||
| Manual Fingerprint Verify | |||||||||||
| MITM-Proof Directory | |||||||||||
| No IP Logging | Impossible | ||||||||||
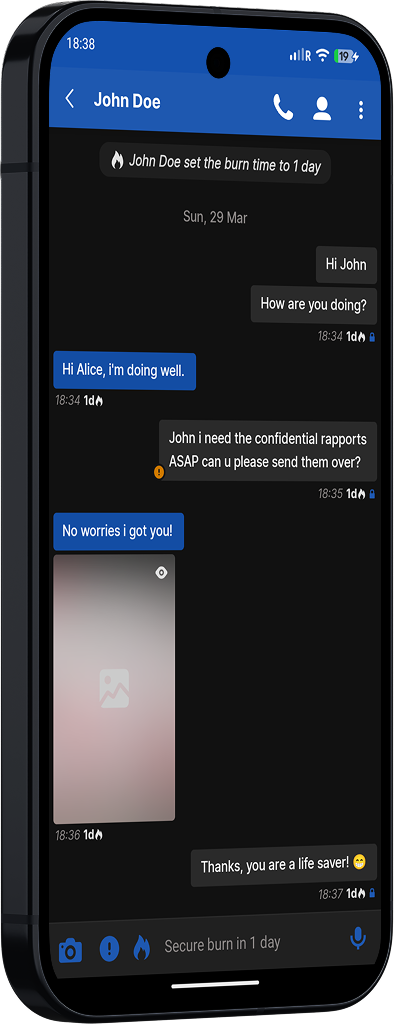
| Self-Destructing Messages | |||||||||||
| Advanced 1:1 Burn Timer | |||||||||||
| Not Implicated in Intel Sharing | |||||||||||
| Privacy Stance | Great | Good | Good | Poor | Poor | Poor | Poor | Good | Poor | Good | Poor |
| Data Collected | None | Contact info & phone # | Contact info & phone # | Extensive | Extensive | Extensive | Extensive | Contacts, identifiers, diagnostics | Contact info, identifiers, phone # | Contact info, identifiers, diagnostics | Extensive |
| Cryptographic Primitives | Curve25519 & sntrup761 XChaCha20-256 Poly1305 |
Curve25519 & Kyber-1024 AES-256 HMAC-SHA256 |
Curve25519 & Kyber-1024 AES-256 HMAC-SHA256 |
Curve25519 AES-256 HMAC-SHA256 |
Curve25519 AES-256 HMAC-SHA256 |
P-256 ECDH & Kyber-768 AES-256 HMAC-SHA384 |
Curve25519 AES-256 HMAC-SHA256 |
Curve25519 AES-256 HMAC-SHA256 |
RSA 2048 AES-256 SHA-256 |
Curve25519 XSalsa20-256 Poly1305 |
Curve25519 Salsa20-128 HMAC-SHA256 |
| Company Jurisdiction | None | USA | USA | USA | USA | USA | USA | UK | USA / UK | Switzerland | Luxembourg / Japan |
| Funding | User subscriptions | Non-profit | Donations | Meta | Apple | Meta | Private | Pavel Durov | User subscriptions | Private |
Not all mobile operating systems are built the same. Here's how our hardened ecosystem measures up.
| Feature |
|
|
|
|
|
|
|---|---|---|---|---|---|---|
| Verified Boot | ||||||
| Kernel Hardening | ||||||
| Memory Hardening | ||||||
| Zero Telemetry | ||||||
| App Isolation | ||||||
| SELinux Enforcement | ||||||
| Reduced Attack Vector: No Bluetooth | ||||||
| Reduced Attack Vector: No Location | ||||||
| Reduced Attack Vector: No GPS | ||||||
| Reduced Attack Vector: No Emergency Services | ||||||
| Reduced Attack Vector: Removed 2G (GPRS) | ||||||
| Duress Password | ||||||
| Panic Button | ||||||
| Remote Wipe | ||||||
| Lock Time Wipe | ||||||
| Stealth Mode | ||||||
| Grab Protection | ||||||
| Faraday Protection | ||||||
| System-wide Live Voice Changer | ||||||
| Built-in Secure Messaging | ||||||
| Data Extraction Impossible by Forensic Tools (AFU) | Difficult |
Find answers to common questions about our secure messaging platform.
CryptoChat is a secure, anonymous communication platform designed from the ground up. It is not just an application, but a complete infrastructure encompassing applications, an operating system, servers, relays, and more.
CryptoChat is designed from the ground up with its own hardened Operating System and infrastructure. Unlike other apps that run on standard Android or iOS, we provide a complete secure ecosystem that doesn't rely on third-party services. Our devices come pre-configured with military-grade security settings, zero metadata collection, and multi-hop routing through privacy-preserving jurisdictions.
Our client base includes high-net-worth individuals (HNWIs), celebrities, politicians, finance and banking professionals, journalists, and anyone who values privacy. These users require absolute confidence that their conversations remain secure, fully encrypted, and leave no trace of ever having taken place.
No. For security reasons, we do not allow users to install any 3th party application or software on our devices. All apps are pre-installed and pre-configured by CryptoChat. This closed ecosystem prevents malicious software, spyware, or vulnerable applications or software from compromising your security. It also eliminates the risk of user error in configuring applications securely.
Yes. For transitional purposes, we provide our own custom hardend opt-in version of Signal for communication with non-CryptoChat users. We strongly advise you to only use this in case your contact does not have CryptoChat, and for the most secure communication, convert them to CryptoChat immediately.
Using your CCID (CryptoChat ID), you can contact your reseller to have your device remotely wiped instantly. All content, encryption keys, data and eSIM’s will be securely erased and rendered unrecoverable. This works even if the device is turned off or in BFU (Before First Unlock) mode. We also offer a duress password that can wipe the device when entered under coercion if needed.
No, when a device is wiped, this means the encryption keys to decrypt all data on the device have been erased, so there is no way back to recover any data that has ever been on the device.
Unfortunately, all data on your device is no longer recoverable without the right password combination. Contact your reseller to have a reset performed and he or she will make your device working again, only without any previous stored data.
No. PGP (Pretty Good Privacy) is an asymmetric encryption protocol developed in 1991 by Philip R. Zimmermann. It was originally designed for securing email communications rather than real-time messaging. While PGP remains a strong and widely respected encryption standard, it does not provide forward secrecy or perfect secrecy. Additionally, it lacks features such as plausible deniability, and if a private key is ever compromised, previously encrypted messages may be decrypted.
CryptoChat uses modern, state-of-the-art cryptographic primitives to ensure secure communication. Messages are encrypted using XChaCha20-Poly1305, an authenticated encryption scheme that provides both confidentiality and integrity with a 256-bit key. For key exchange, CryptoChat utilizes Curve25519 (X25519) ECDH alongside SNTRUP761, a post-quantum key encapsulation mechanism, in a hybrid approach designed to offer strong security against both classical and potential future quantum attacks. This combination of well-established and forward-looking cryptographic techniques is widely regarded as highly secure and suitable for modern high level secure messaging systems.
Multi-hop routing is a privacy-enhancing technique where messages are relayed through multiple independent relays before reaching their final destination. In CryptoChat’s implementation, messages pass through a triple-hop relay system, meaning they traverse three separate servers along the way.
This design ensures that no single server has full knowledge of both the sender and the recipient. Each relay only knows the immediate node it received the message from and the next node it forwards it to, but never the complete path. As a result, it becomes extremely difficult to correlate who is communicating with whom.
Combined with the fact that we do not maintain user identifiers or logs, this architecture prevents us or any intermediary from linking messages to specific users. Even in theory, a single point of observation cannot reconstruct the full communication path, providing the strongest level of anonymity and protection possible.
No. CryptoChat is designed with multiple safeguards to prevent unauthorized manipulation. Updates cannot be delivered to user devices unless they are verified through a strict multi-signature process, requiring approval from multiple trusted members of our team. Any attempt by an adversary to distribute a malicious or unauthorized update would be automatically rejected by the device.
Additionally, even in the unlikely event that a server were compromised, it would not expose user data. Our servers operate solely as relay nodes and do not store sensitive information. All data passing through them is end-to-end encrypted, meaning it remains unreadable and inaccessible to the server itself or any third party.
No. We do not have access to or store any information related to our clients’ chat accounts, contacts, encryption keys, passwords, messages, notes, or other personal data. The only information we retain is whether a CCID remains valid until the end of the subscription period. Even this data is not linked to any chat or eSIM details. As a result, we are unable to provide such information because we simply do not possess it. All messages are end-to-end encrypted and all encryption keys never leave a device.
No. As stated in previous responses, we do not have access to any client information and we do not maintain logs. Even if we intended to do so, it is technically impossible for us to access or retrieve such data.
CryptoChat operates its own Mobile Device Management (MDM) software to effectively manage and secure all encrypted handsets. Our MDM solution is fully developed in-house, allowing us to maintain complete control over its functionality, security standards, and data handling processes.
By not relying on any third-party providers, we ensure a higher level of privacy, flexibility, and customization tailored specifically to our operational needs. This approach also enables us to respond quickly to security challenges, implement updates efficiently and securely, and continuously improve our system in line with evolving industry standards.
CryptoChat exclusively uses its own in-house developed Mobile Device Management (MDM) system to manage Android secure device policies. This dedicated solution allows us to enforce strict security configurations and maintain full control over device management processes.
Our MDM system ensures that all devices running CryptoChat consistently meet our security standards and compliance requirements. By managing everything internally, we can rapidly implement security updates, address potential vulnerabilities, and adapt our policies to meet evolving security demands.
CryptoChat features a custom designed secure networking architecture built to protect user privacy at a deeper level. Rather than relying on traditional VPN solutions or any 3th party VPN providers, we have developed our own multi-relay hop system to enhance both security and anonymity.
This approach routes communication through multiple layers, reducing the risk of tracking or interception and providing stronger protection against network-level threats. While VPNs can offer a basic layer of privacy, they are not sufficient on their own to ensure true security.
At CryptoChat, we emphasize end-to-end encryption combined with advanced network anonymization techniques, ensuring that user conversations remain private, secure, and resilient against evolving threats.
No, this practice does not provide any meaningful security benefit and is highly unintuitive for most users.
When you change an IMEI, often referred to as “flashing,” it is essential to also replace your SIM card before reconnecting to a mobile network. If you do not, the telecom provider may associate your new IMEI with your previous IMSI, effectively linking the two and undermining the intended purpose of changing the device identifier.
To achieve a higher level of privacy, all connections would need to be disabled, the SIM card replaced, and the IMEI changed before reconnecting to a network. Even then, this approach remains complex, impractical, and in many jurisdictions, illegal.
Any service claiming to offer instant IMEI changes without requiring a reboot or at least a noticeable interruption in network connectivity is misleading and should not be trusted.
Legitimate modification of device identifiers involves low-level system changes that cannot occur seamlessly while the device remains fully connected to a network. Claims suggesting otherwise are often indicative of ineffective or fraudulent solutions that fail to deliver real functionality or security benefits.
Users should exercise caution and avoid relying on such services, as they may provide a false sense of security and potentially expose devices to additional risks.
CryptoChat standardizes on Google Pixel devices due to their advanced hardware security capabilities. These devices incorporate the Titan M2 security chip, which supports features such as verified boot, hardware-backed key storage, and enhanced protection against physical tampering.
Google Pixel devices also offer timely security updates and clearly defined support lifecycles, which are critical for maintaining a secure and compliant environment. In addition, the Pixel platform provides the flexibility required to deploy and maintain our custom operating system in a controlled and reliable manner.
This combination of hardware security, software integrity, and long-term support aligns with CryptoChat’s requirements for delivering a secure and trustworthy communication platform.
CryptoChat supports devices only for as long as they continue to receive official security updates from the manufacturer. Once these updates are discontinued, we can no longer ensure that the device meets our security standards. As a result, support for that model is also discontinued to maintain the highest level of security for our users.
No. CryptoChat, along with all authorized resellers, only provides brand-new devices that have never been used before. This ensures the integrity, security, and reliability of the hardware from the outset.
Battery life depends largely on the device model you choose. Older or entry-level models typically offer around two days of usage on a single charge, while higher-end models can provide approximately three to four days of battery life under average usage conditions. Actual performance may vary based on usage patterns and settings.
Your network connection may be slow if you are in an area with poor signal strength or limited to a 2G network. Performance can also be affected by temporary network outages or if you are outside the coverage area of CryptoChat cellular network.
In such cases, reduced speeds, higher latency, or intermittent connectivity may occur. For the best experience, we recommend using CryptoChat in areas with strong network coverage and a stable connection.
You can check our network coverage by clicking here.
Yes, CryptoChat is compatible with all MiFi and WiFi routers. It can connect to any wireless network while maintaining a strong focus on user privacy.
For each connection, CryptoChat uses a randomized MAC address and device name, helping to reduce the risk of device tracking across networks. This adds an additional layer of anonymity when connecting to different WiFi environments.
Our networking infrastructure is designed to provide consistent security and anonymity, whether you are using cellular data or a WiFi connection. This ensures that your communications remain protected regardless of how you access the network.
Questions about devices, shipping, reseller coverage, or secure setup? Reach us through encrypted channels first, or use email for standard support requests.
If you already know which encrypted app you prefer, use it directly below. If not, Signal is the easiest starting point for most people, while Simplex and Session are better when you want less identity exposure.
Share the basics and our team will reply with the right next step.
Each option below goes to the CryptoChat team. Pick the channel that fits your comfort level and device setup.
+57 300 3122282
Open WhatsAppMessage us on WhatsApp for general inquiries, order questions, and regular support requests.
Secure, familiar, and fast for direct conversations with our team.
Open SignalA strong choice if you want encrypted messaging with a simpler onboarding flow.
A solid option when you want a more identity-minimized messaging flow.
Open SimplexBest if anonymity matters more than convenience in your initial contact.
Private messaging through a decentralized network for users already in Session.
Open SessionUseful if you already operate inside the Session ecosystem and want continuity there.
Small details make support smoother and keep your outreach cleaner from the start.
Start with the minimum useful details. You can always provide more information later if we need it.
Your country or city is usually the fastest way for us to connect you to the right reseller or support path.
Tell us whether you want to buy, renew, troubleshoot, or discuss partnering so we can respond with the right next step.
Explore current devices, compare options, and reach out when you want a guided recommendation.
Build a high-trust offer for clients who need secure devices, dependable onboarding, and responsive partner support. We keep the product focused so you can focus on relationships and delivery.
Ideal for resellers, boutique security firms, concierge providers, and privacy-focused operators who want a differentiated secure-device offer.
Fill out the form below and our team will get back to you shortly.
Select your region to connect with authorized resellers and secure your communications.
Search or select a country to view reseller details for that market.
No countries match your search.
Select a region on the map or from the list above to view reseller information for that area.
For purchases and support in , please contact your local reseller or reach us directly through any of the channels below.